Technology
Google says China and Iran tried to hack Biden and Trump’s campaigns


Google has announced it has identified state-sponsored hacking attempts upon both Biden and Trump’s campaign staff, originating from China and Iran respectively. Fortunately, both attacks appear to have failed.
“Recently [Google’s Threat Analysis Group] saw China APT group targeting Biden campaign staff & Iran APT targeting Trump campaign staff with phishing,” Google’s threat analysis director Shane Huntley tweeted on Thursday. “No sign of compromise. We sent users our govt attack warning and we referred to fed law enforcement.”
APT stands for “advanced persistent threat,” meaning a lengthy and targeted cyberattack campaign intending to covertly gain access to a computer network. These campaigns can take place over months or years, and typically remain focused on an individual target.
Recently TAG saw China APT group targeting Biden campaign staff & Iran APT targeting Trump campaign staff with phishing. No sign of compromise. We sent users our govt attack warning and we referred to fed law enforcement. https://t.co/ozlRL4SwhG
— Shane Huntley (@ShaneHuntley) June 4, 2020
A Google spokesperson confirmed the phishing attacks from Chinese and Iranian groups, and reiterated that they found no evidence the attempts were successful. The matter has now been referred to U.S. law enforcement. “We encourage campaign staff to use extra protection for their work and personal emails,” the spokesperson said in a statement.
Huntley concurred. “If you are working on a campaign this election cycle, your personal accounts may be targeted,” he tweeted, linking to a Google blog from February on election security. “Use the best protection you can. Two factor authentication or Advanced Protection really can make a difference.”
Enabling two-factor authentication is good security advice for anyone, even if you aren’t working on a U.S. presidential election campaign.
In phishing attempts such as the ones used in these attacks, hackers falsely present themselves as trustworthy entities to lure their victims into clicking malicious links or downloading dangerous software. Doing so will typically give the hacker access to sensitive information. These attacks are most commonly carried out via email, however instant messaging can also be used.
Both Biden and Trump’s campaigns confirmed that they had been made aware of the recent phishing attacks.
A spokesperson for Biden’s campaign stated it was prepared for such hacking attempts, having known they were likely to occur. “Biden for President takes cybersecurity seriously, we will remain vigilant against these threats, and will ensure that the campaign’s assets are secured.”
A Trump campaign spokesperson also stated they are “vigilant about cybersecurity.”
Huntley tweeted that the groups involved in the attacks on the Biden and Trump campaigns were China’s APT31, also known as Zirconium, and Iran’s APT35, also known as Newscaster Team. Both have previously been accused of targeting U.S. organisations or government agencies.
This is far from the first time state-sponsored hackers have allegedly attempted to breach foreign governments’ computer networks, and it won’t be the last. Of course, governments routinely deny any involvement in such attacks.
-
 Business7 days ago
Business7 days agoXaira, an AI drug discovery startup, launches with a massive $1B, says it’s ‘ready’ to start developing drugs
-

 Entertainment6 days ago
Entertainment6 days agoSummer Movie Preview: From ‘Alien’ and ‘Furiosa’ to ‘Deadpool and Wolverine’
-

 Business6 days ago
Business6 days agoPetlibro’s new smart refrigerated wet food feeder is what your cat deserves
-
 Entertainment4 days ago
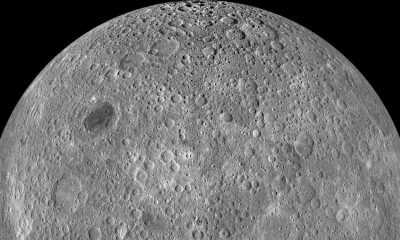
Entertainment4 days agoWhat’s on the far side of the moon? Not darkness.
-

 Business5 days ago
Business5 days agoHow Rubrik’s IPO paid off big for Greylock VC Asheem Chandna
-

 Business5 days ago
Business5 days agoThoma Bravo to take UK cybersecurity company Darktrace private in $5B deal
-

 Business4 days ago
Business4 days agoTikTok faces a ban in the US, Tesla profits drop and healthcare data leaks
-

 Business6 days ago
Business6 days agoZomato’s quick commerce unit Blinkit eclipses core food business in value, says Goldman Sachs






















